IMAP component for .NET
Mail.dll email component includes an excellent IMAP email component. Unleash the full potential of email management with Mail.dll’s outstanding IMAP email component.
It offers .NET developers an unparalleled tool for handling IMAP email protocol. From retrieving messages to managing folders and attachments, the IMAP component in Mail.dll simplifies complex tasks into user-friendly functions.
Mail.dll is available for all regular .NET framework versions as well as for most recent .net 6, 7 and .net 8 and higher.
IMAP, short for Internet Message Access Protocol, is one of the two most prevalent Internet standard protocols for e-mail retrieval, the other being Post Office Protocol – POP3 (also available in Mail.dll).
IMAP has many advantages over POP3, most important are using folders to group emails, saving seen/unseen state of the messages and search capability.
This article is going to show how easy is to connect to use IMAP client from .NET, download and parse unseen messages.
Installation
The easiest way to install Mail.dll is to download it from nuget via Package Manager:
PM> Install-Package Mail.dll
Alternatively you can download Mail.dll directly from our website.
Connect to IMAP
First you need connect to IMAP server. You should use Imap class for that. Using block ensures that IMAP connection is properly closed and disposed when you’re done.
using(Imap imap = new Imap())
In most cases you should be using TLS secured connection – ConnectSSL method will choose a correct port and perform SSL/TLS negotiation, then you perform IMAP authentictation:
imap.ConnectSSL("imap.server.com");
imap.UseBestLogin("user", "password");
Mail.dll supports OAuth 2.0 for authentication, you can find OAuth2 samples for Office365 and Gmail on the Mail.dll samples page.
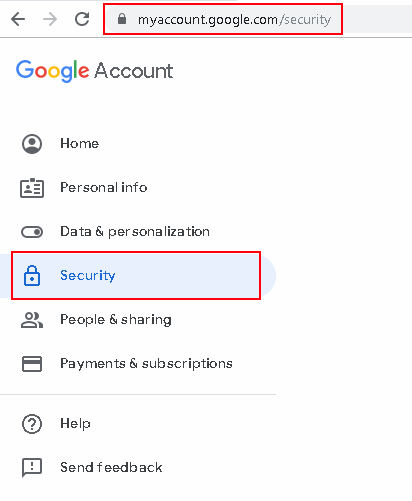
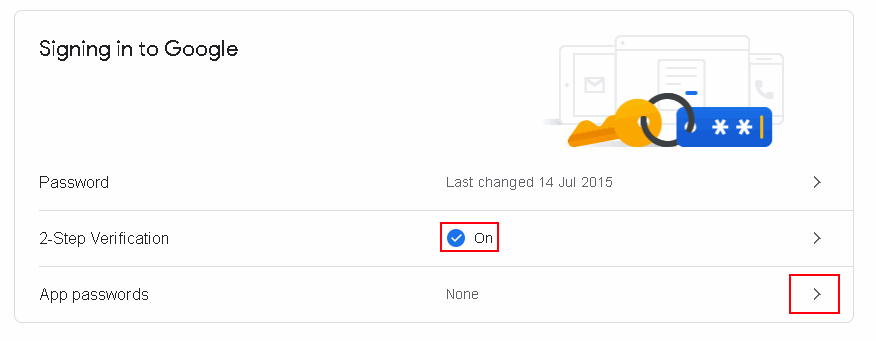
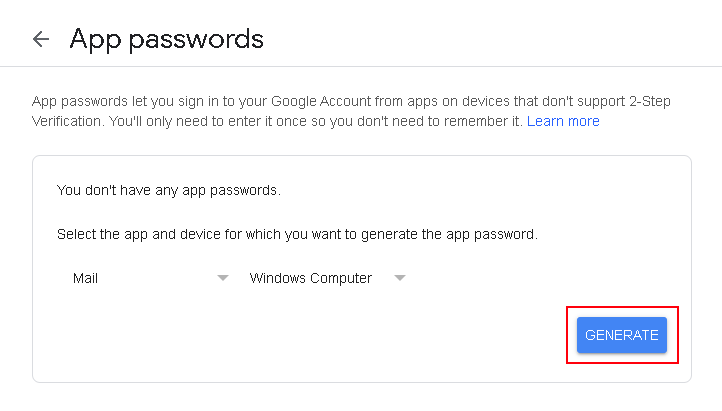
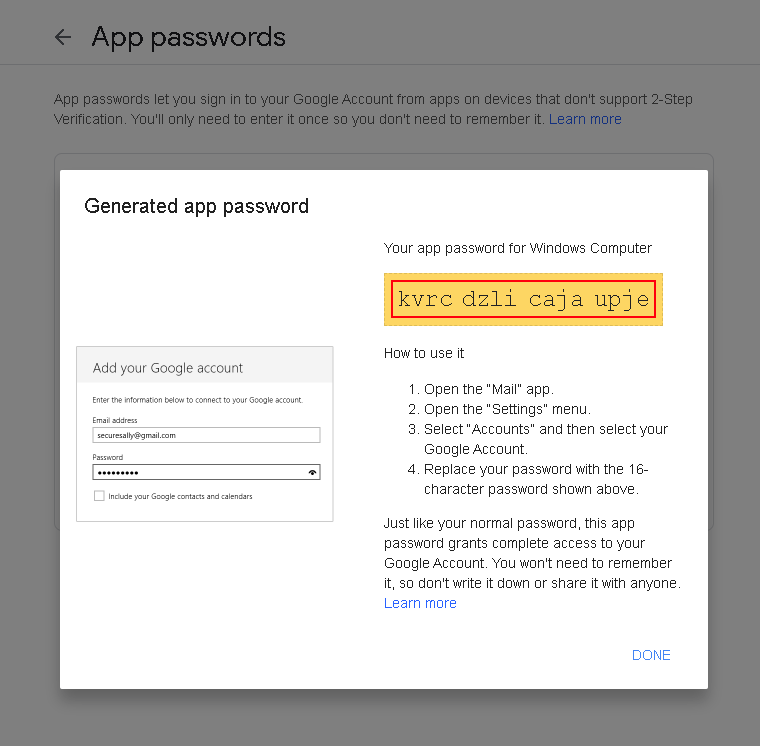
For Gmail you may want to use Gmail’s App Passwords.
Search for unseen emails
As IMAP groups messages into folder you need to select a well know INBOX folder. All new, received emails are first placed in the INBOX folder first:
imap.SelectInbox();
Then you perform a search that find all unseen messages
List<long> uids = imap.Search(Flag.Unseen);
Download and parse emails
Finally you download emails one-by-one and parse them. You should use MailBuider class to parse emails:
var eml = imap.GetMessageByUID(uid);
IMail email = new MailBuilder().CreateFromEml(eml);
Entire code to download emails in .net
Entire code to download emails using IMAP is less than 20 lines:
using(Imap imap = new Imap())
{
imap.ConnectSSL("imap.server.com"); // or Connect for no TLS
imap.UseBestLogin("user", "password");
imap.SelectInbox();
List<long> uids = imap.Search(Flag.Unseen);
foreach (long uid in uids)
{
var eml = imap.GetMessageByUID(uid);
IMail email = new MailBuilder().CreateFromEml(eml);
string subject = mail.Subject;
}
imap.Close();
}
and for those who like VB.NET more:
Using imap As New Imap()
imap.ConnectSSL("imap.server.com")
imap.UseBestLogin("user", "password")
imap.SelectInbox()
Dim uids As List(Of Long) = imap.Search(Flag.Unseen)
For Each uid As Long In uids
Dim mail As IMail = New MailBuilder()_
.CreateFromEml(imap.GetMessageByUID(uid))
Console.WriteLine(mail.Subject)
Next
imap.Close()
End Using
It can’t get much simpler than that!
Summary
You can use Mail.dll .NET IMAP component to:
- Create, delete and rename IMAP folders
- Download and upload emails
- Download email attachments
- Move and copy email messages between folders
- Flag messages
- Powerful IMAP search with easy to use syntax
- parse emails using fully tested (over 6000 unit tests) Mail.dll .NET email parser
It works perfectly with Exchange, Office365, Gmail and all other IMAP servers.
Just give Mail.dll a try and download it at: Mail.dll .NET IMAP component
Get Mail.dll